SAP Security Research Group focuses on security issues relevant to SAP R/3, Netweaver / BW infrastructures and applications.
Fixed Vulnerabilities:
SAP has released security patches for fixing the issues we have reported. SAP’s acknowledgements can be found here.
SAP Note 1484692 – Protect read access to password hash tables
SAP Note 1497104 – Protect access to PSE
SAP Note 1421005 – Secure configuration of the message server
SAP Note 1483525 – New security center in SAP GUI 7.20
SAP Note 1485029 – Protect read access to key tables
SAP Note 1488406 – Handling the generated user TMSADM
SAP Note 1511107 – Executing freely determined code using transaction SE37
SAP Note 1510704 – Missing Authorization Check in AFX Workbench report
Areas of Interest:
- SAP Secure Infrastructure Design
- Gateway Security
- Cryptography Implementations in SAP systems
- ABAP Injection
- SAP Rootkits
- SNC(Secure Network Communications) / SSO (Single Sign-on) Attacks
- Database Attacks
- EDI/IDOC Manipulation
- Usable Hardening Practices
- Credential Theft in SAP Systems
- SAPGUI Vulnerabilities
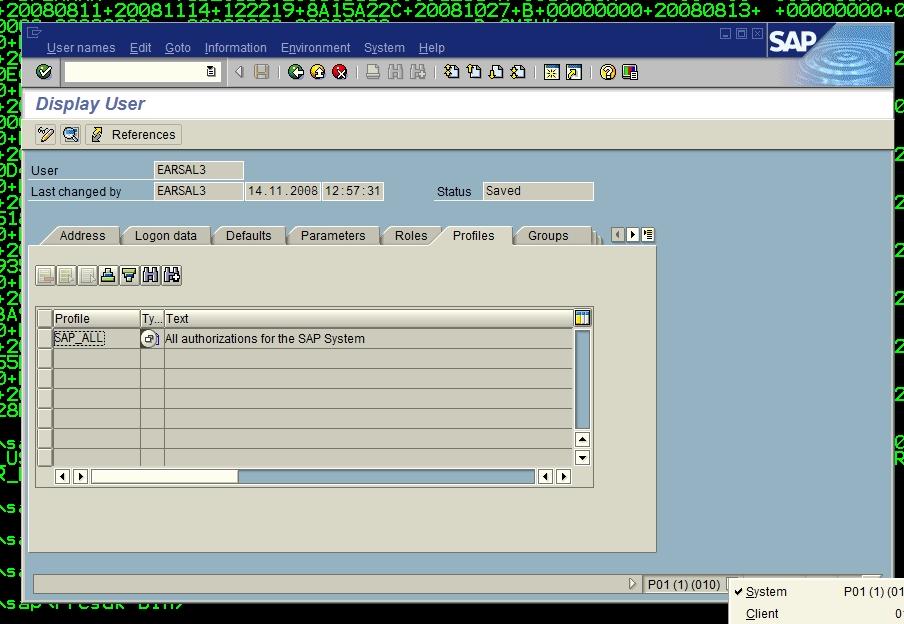
- SAP Authorizations Weaknesses
Graduate and undergraduate students can apply to participate in SAP Security Research Group.
Requirements:
Solid Understanding of Network Protocols
Fluent C++, C# or Java programming.
Please apply to ertunga @ sabanciuniv.edu if you’d like to research/develop/break/fix (not necessarily in that order) with us by sending a short information about you and your availability.
Links
5 important SAP security recommendations
SAP authorizations concept
SAP GUI security
SAP Audit Tools
SAP audit
SAP penetration testing
ABAP security
Enterprise Threat Detection for SAP Systems
SAP vulnerability scanner
SAP SIEM – Security Event Management Integration
SAP Splunk
Splunk and SAP event correlation using Splunk HTTP connector.
SAP QRadar
IBM QRadar SAP offense pre-correlation using QRadar Leef format with SAP transactional data.
SAP ArcSight
SAP SIEM
Native SAP security monitoring
What is SAP and GDPR
What is EU General Data Protection Regulation (GDPR) and how it affects SAP systems
—–
This website contains references to products of SAP AG. SAP, ABAP and other named SAP products and associated logos are brand names or registered trademarks of SAP SE in Germany and other countries in the world.